History of Privacy Timeline
-
1789
U.S. Constitution
The U.S. Constitution came into effect in 1789. While not explicitly guaranteeing the right to privacy, the Supreme Court has found that the Constitution does provide for a right to privacy in its First, Third, Fourth, and Fifth amendments.
-

1890
Brandeis "Right to Privacy" Law Review Article
The Right to Privacy (or “the right to be let alone”) is a law review article published in the 1890 Harvard Law Review. Written primarily by Justice Louis Brandeis (but credited to both Brandeis and Samuel Warren), it is one of the most influential essays in American legal history and is considered the first publication in the U.S. to argue for a right to privacy. The authors charge that “instantaneous photographs and newspaper enterprise have invaded the sacred precincts of private and domestic life” and seek to “consider whether the existing law affords a principle which can properly be invoked to protect the privacy of the individual.”
-
1914
Establishment of the FTC
The Federal Trade Commission Act (FTCA) of 1914 established the Federal Trade Commission and outlawed unfair or deceptive commercial practices. Since the 1970s, the FTC has been the leading federal agency that is most often involved with privacy issues, regulations, and enforcement.
-

1917
Ruling on Protection of Sealed Mail
In the second decade of the 20th century, the newly established Bureau of Investigations was actively working on investigating acts of foreign sabotage and rooting out subversion. Surveillance extended to monitoring and illegally opening correspondence of suspected subversives. When the bureau filed an official request to open mail, Solicitor General Judge William Lamar ruled against the privacy infringement and upheld long-established protections of sealed mail.
-
1948
George Orwell Writes 1984
1984 is a dystopian novel written by George Orwell containing themes of nationalism, futurology, censorship, and surveillance. Inhabitants of Oceania, the “super-state” where the book takes place, have no privacy. Public and private spaces are filled with cameras and microphones. Even thought is controlled by undercover agents of the “Thought Police.”
-

1948
U.N. Declaration of Human Rights
Proclaimed by the United Nations General Assembly on December 10, 1948, the U.N. Declaration of Human Rights (UDHU) was drafted by representatives from all over the world with a variety of legal and cultural backgrounds. Article 12 states that “No one shall be subjected to arbitrary interference with his privacy, family, home or correspondence, nor to attacks upon his honour and reputation. Everyone has the right to the protection of the law against such interference or attacks.”
-

1960
Privacy Torts
In 1960, William L. Prosser, a well known legal scholar of the time, published the article Privacy. In the article, still considered influential in the field of privacy law today, he outlined four torts that would allow someone whose privacy was violated in one of those four ways to sue the perpetrator for damages. These torts are still used today:
- Intrusion upon seclusion or solitude, or into private affairs;
- Public disclosure of embarrassing private facts;
- Publicity which places a person in a false light in the public eye; and
- Appropriation of one’s name or likeness.
-
1967
Alan Westin Writes Privacy and Freedom
Alan Westin, who defined privacy as “the claim of individuals … to determine for themselves when, how and to what extent information about them is communicated,” helped set the stage for modern debates about technology, privacy, and personal freedom. His book, Privacy and Freedom, is still one of the seminal works on privacy to this day.
-

1960s and '70s
Supreme Court Rulings Related to Privacy
- Griswold v. Connecticut (1965) was a landmark Supreme Court case involving a Connecticut “Comstock law” that prohibited all forms of contraception. By a vote of 7-2, the Supreme Court ruled against the law on the basis of the “right to marital privacy,” laying the foundation for the right to privacy with regard to intimate practices.
- Katz v. United States (1967), a landmark decision the Supreme Court, extended Fourth Amendment protections against unlawful searches and seizures beyond citizens' homes and property to anywhere a person has a reasonable expectation of privacy.
- Eisenstadt v. Baird (1972) was a U.S. Supreme Court case that guaranteed the right of unmarried people to possess contraception. The ruling was based on the right to privacy established in Griswold v. Connecticut and the Equal Protection Clause of the Fourteenth Amendment.
-

1972
In United States v. U.S. District Court, 407 U.S. 297 (Keith Case) the United States Supreme Court ruled unanimously that warrants are required for domestic intelligence surveillance.
-
1973
Records, Computers and the Rights of Citizens: Report of the HEW Advisory Committee on Automated Personal Data Systems
The Department of Health, Education, and Welfare (HEW) Secretary’s Advisory Committee on Automated Personal Data Systems (SACAPDS) developed the landmark 1973 Records, Computers and the Rights of Citizens, Report of the Secretary’s Advisory Committee on Automated Personal Data Systems. The report was the origin of Fair Information Practices, a set of principles that formed the basis for modern privacy legislation.
-

1974
FERPA Student Privacy
FERPA, the Family Educational Rights and Privacy ACT of 1974, or Buckley Amendment, is a federal law that safeguards the privacy of student education records. The law applies to all schools, colleges, universities, and other institutions that receive funds from the U.S. Department of Education.
-
1974
Privacy Act of 1974
Enacted December 31, 1974, the Privacy Act of 1974 is a U.S. federal law establishing a Code of Fair Information Practice on federal agencies’ collection, maintenance, use, and dissemination of personally identifiable information.
-
1977
Privacy Commission Report
Established in Section 5 of the Privacy Act of 1974, the U.S. Privacy Protection Study Commission was tasked with evaluating the Privacy Act and issuing a report containing its findings and recommendations for improvement. The Commission issued its final report and ceased operation in 1977.
-

1986
TCPA and National Do Not Call Registry
The Telephone Consumer Protection Act (TCPA) and the National Do Not Call Registry regulate telemarketing calling and automated telephone dialing. The TCPA prohibits certain types of solicitation calls, while the Do Not Call Registry allows consumers to opt out of telemarketing calls.
-

1991
Common Rule Human Subject Research Privacy
In 1991, revisions were made to the U.S. Department of Health and Human Services Title 45 CFR 46 (Public Welfare) Subparts A, B, C and D. Subpart A, known as The Common Rule, is an updated version of a 1981 rule of ethics in the United States concerning biomedical and behavioral research involving human subjects. It was adopted by Institutional Review Boards for oversight of human research and is the standard of ethics guiding all government funded (and most non government funded) research in the U.S. The regulation was last updated in 2018.
-

1995
EU Data Protection Directive
Adopted by the European Union in 1995, the Data Protection Directive regulates the processing of personal data within the EU. In comparison to the United States, the right to privacy is a more highly developed field of law in the EU. The Data Protection Directive was superseded by the General Data Protection Regulation (GDPR) in 2018.
-

1996
HIPAA Health and Medical Privacy
HIPAA, or the Health Insurance Portability and Accountability Act of 1996, was created to streamline the flow of healthcare information, protect Personally Identifiable Information maintained by the healthcare and health insurance industries from theft and fraud, and deal with limitations on health insurance coverage. Also known as the Kennedy-Kassebaum Act, it was put in place by the 104th United States Congress and signed by President Bill Clinton.
-

1998
COPPA Children's Online Privacy
COPPA, or the Children’s Online Privacy Protection Act, became U.S. federal law on October 21, 1998. It pertains to the online gathering of personal data by entities in the U.S. about children under 13 years of age, both in and out of the U.S. It includes information about what websites must include in their privacy policies, how to verify consent from parents or guardians, and how sites should protect children’s safety and privacy online.
-

1999
Chief Counselor for Privacy in Federal Government
Before U.S. government agencies had Chief Privacy Counselors, they had Privacy Act Officers. They primarily dealt with requests from individuals for their government records under the access provisions of the Privacy Act and the Freedom of Information Act (FOIA). Realizing the need for a more effective position, the Clinton administration began requiring agencies to designate a Chief Privacy Counselor. Peter Swire was named the Chief Privacy Counselor for the administration within the Office of Management and Budget.
-

1999
Gramm Leach Bliley Act
The Gramm-Leach-Bliley Act (GLBA), or the Financial Modernization Act of 1999, is a federal law requiring disclosure by financial institutions of how they share and protect private customer data. The law requires financial institutions to explain how customer data is shared, provide an opportunity for customers to opt out of having their info shared, and protect private data with a security plan created by the institution. The core of the data protections are outlined in the GLBA’s Safeguards Rule. Implementation of the act was driven and enforced by the Federal Trade Commission’s Privacy of Consumer Financial Information Rule (Privacy Rule), federal banking agencies and other federal regulatory authorities, and state insurance oversight agencies.
-

1999
First Chief Privacy Officer
A Chief Privacy Officer (CPO) is a senior level executive responsible for managing risk related to and ensuring compliance with information privacy laws. The role exists in an increasing number of corporations, public agencies, and other organizations. While the first example of a CPO can be found with the 1991 implementation of the role at the consumer database marketing company Acxiom, it became more well known with the 1999 hiring of privacy lawyer Ray Everett by the internet advertising technology firm AllAdvantage.
-

2001
Following the terrorist attack on September 11, Congress enacted the Uniting and Strengthening America by Providing Appropriate Tools Required to Intercept and Obstruct Terrorism (USA PATRIOT) Act. In the name of national security, the act expands the government’s authority to monitor phone and email communications. In 2006, 14 of the original provisions planned to be sunset were made permanent under the USA PATRIOT Act Improvement and Reauthorization Act.
-
2002
E-Government Act of 2002
The E-Government Act of 2002 was passed by Congress in an effort to bring the federal government into the 21st century by applying advances in information technology to improve access to and use of government services and information. A central part of the legislation was the requirement for all federal government agencies to perform a Privacy Impact Assessment (PIA) for any new technology that “collects, maintains, or disseminates personally identifiable information (PII), or for a new aggregation of information that is collected, maintained, or disseminated using information technology.”
-
2003
State Data Breach Notification Laws
In 2003, California was the first state to implement data breach notification laws. The new legislation required businesses and state agencies to disclose when Californian’s personal information was exposed in a security breach. Most other states in the U.S. and some jurisdictions abroad have modeled their data breach disclosure laws after this legislation.
-

2004
The Intelligence Reform and Terrorism Prevention Act (IRTPA) amended the National Security Act of 1947 and created the position of “Civil Liberties Protection Officer” within the Office of the Director of National Intelligence.
-

2010
Red Flags Identity Theft Protection
In 2008, the Federal Trade Commission (FTC) and National Credit Union Administration (NCUA) created the Red Flags Rule. The rule was designed to help prevent identity theft. Despite being passed in January 2008, enforcement was delayed until December 31, 2010, due to push-back from opposition.
-

2012
EU Right to be Forgotten
The European Commission in 2012 released a draft European Data Protection Regulation that would supersede the EU Data Protection Directive. The law allows EU citizens to submit requests to search engines to have personal information delinked from the results of searching their name.
-

2018
GDPR
The General Data Protection Regulation (GDPR) is a law dealing with data protection and privacy that went into effect in the European Union (EU) and the European Economic Area EEA) on May 25, 2018. It also applies to the transfer of personal data outside of the EU and EEA.
-

2020
CCPA
The California Consumer Privacy Act (CCPA) is a state statute intended to regulate how businesses handle the personal information of residents of the state of California. The CCPA was signed into law in 2018 and went into effect on January 1, 2020.
-

2021
State Privacy Laws
On March 2, 2021, Virginia’s Governor signed the Consumer Data Protection Act into law. Following California, Virginia became the second state to enact major privacy legislation of general applicability in the United States. The CDPA went into effect on January 1, 2023.
On July 8, 2021, the state of Colorado officially enacted the Colorado Privacy Act. The law went into effect on July 1, 2023.
-
2024
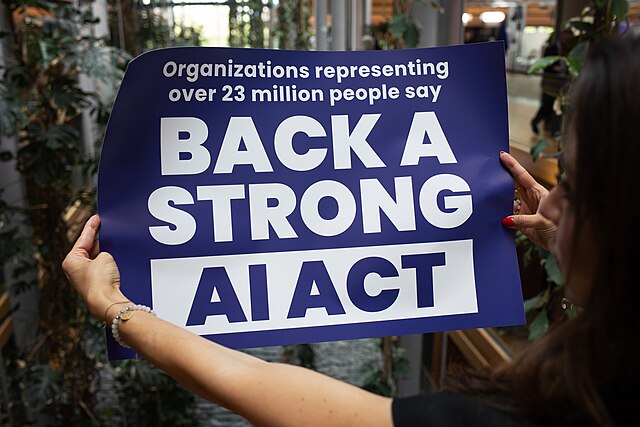
The EU AI Act
The AI Act is a European regulation on artificial intelligence (AI) – the first comprehensive regulation on AI by a major regulator anywhere. The Act assigns applications of AI to three risk categories. First, applications and systems that create an unacceptable risk, such as government-run social scoring of the type used in China, are banned. Second, high-risk applications, such as a CV-scanning tool that ranks job applicants, are subject to specific legal requirements. Lastly, applications not explicitly banned or listed as high-risk are largely left unregulated.
-

2025
State AI Laws
As of March 2025, California, Colorado, and Utah have all passed laws around the use of AI. California’s Law AB 2013 requires AI developers to post information regarding the data used to train their AI systems. The Colorado Artificial Intelligence Act, which goes into effect in February 2026, focuses on high-risk artificial intelligence systems and is designed to protect against algorithmic discrimination in AI systems. The Utah Artificial Intelligence Policy Act imposes disclosure requirements for companies that use generative AI tools.
This is only the beginning of AI regulation throughout the United States. Over 15 other states have proposed AI laws that are working their way through the legislative system.
